AI Conversation
IT Cybersecurity

Did you know that Bahrain is the first country in the Arab world to enact a comprehensive data protection law, the Personal Data Protection Law? This law aims to safeguard individuals' personal information and enhance cybersecurity measures in the country.
https://www.youtube.com/watch?v=hXSFdwIOfnE
data encryption

https://www.youtube.com/watch?v=LA3fah6i-4A
Data encryption is a crucial aspect of cybersecurity, ensuring that sensitive information is protected from unauthorized access. It involves encoding data into a secure format that can only be decoded with the correct key. Encryption helps safeguard data during transmission and storage, enhancing overall cybersecurity measures.
firewalls
https://www.youtube.com/watch?v=9GZlVOafYTg
Firewalls are essential cybersecurity tools that monitor and control incoming and outgoing network traffic based on predetermined security rules. They act as a barrier between trusted internal networks and untrusted external networks, protecting against unauthorized access and cyber threats. Firewalls are crucial for safeguarding sensitive data and preventing cyber attacks.
security training

Security training in IT cybersecurity is essential for professionals to understand and mitigate cyber threats effectively. It covers topics such as network security, encryption, risk management, and incident response. Through hands-on exercises and simulations, individuals learn to protect systems, data, and networks from potential cyber attacks.
https://www.youtube.com/watch?v=Yu0zwqMeLCQ
security policies
.jpg#keepProtocol)
Security policies in IT cybersecurity outline rules and procedures to protect digital assets from unauthorized access, breaches, and threats. They define roles, responsibilities, and guidelines for implementing security measures such as encryption, access controls, and incident response protocols to safeguard sensitive information and ensure data integrity and confidentiality.
https://www.youtube.com/watch?v=5kY9kvzeWjA
incident response plan

An incident response plan in cybersecurity outlines procedures to detect, respond, and recover from security breaches. It includes roles and responsibilities, communication protocols, and steps to mitigate damage. Regular testing and updates are crucial to ensure effectiveness in addressing cyber threats promptly and effectively.
https://www.youtube.com/watch?v=fU_w8Ou9RVg
vulnerability assessment

Vulnerability assessment in IT cybersecurity involves identifying, evaluating, and prioritizing weaknesses in systems to prevent potential threats. It helps organizations understand their security posture, address vulnerabilities proactively, and enhance overall resilience against cyber attacks, ensuring a robust defense mechanism to safeguard sensitive data and systems.
https://www.youtube.com/watch?v=hIbkwnOteTc
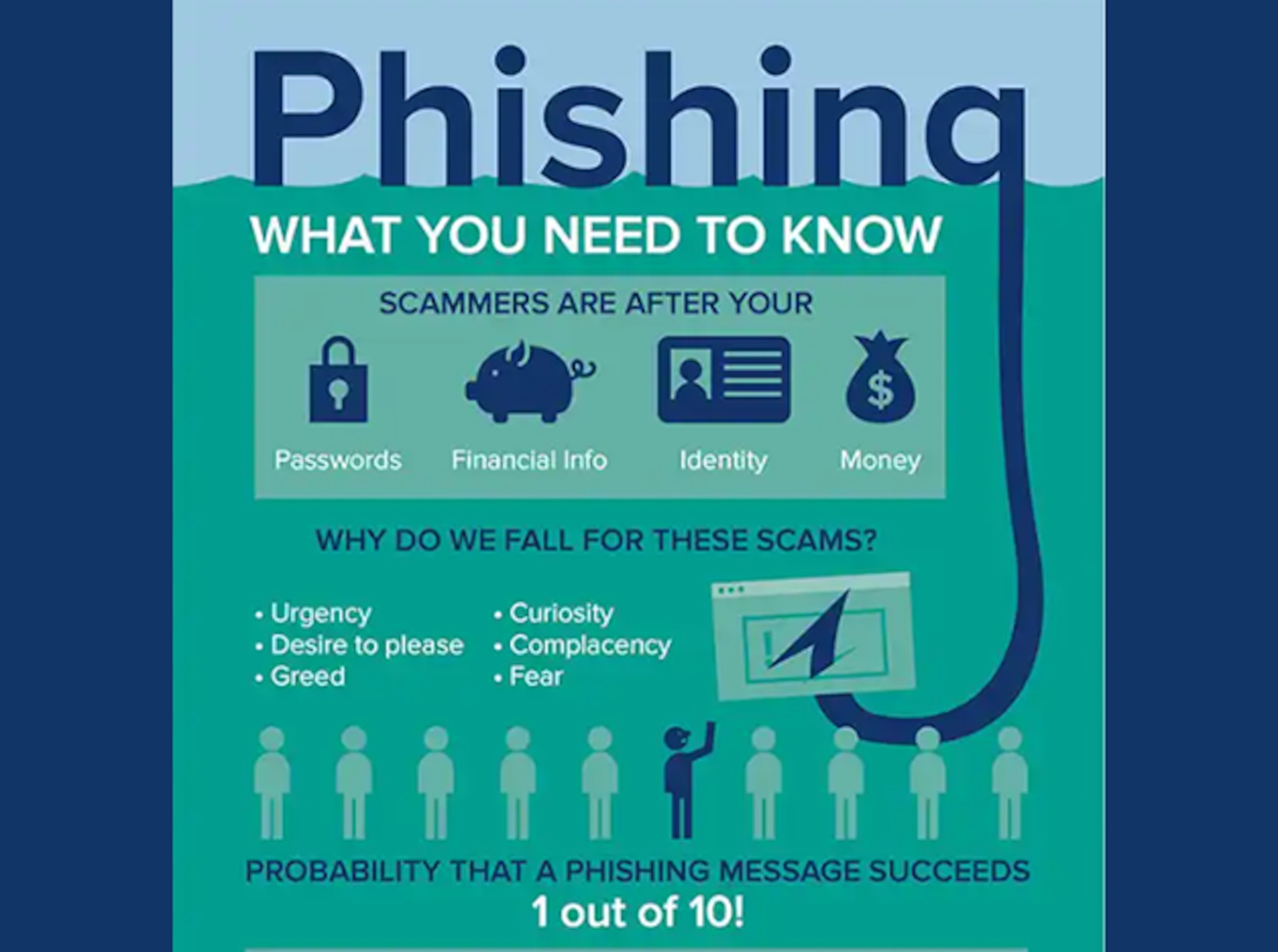
phishing awareness
https://www.youtube.com/watch?v=WNVTGTrWcvw
Phishing awareness is crucial in IT cybersecurity to prevent unauthorized access to sensitive information. It involves recognizing and avoiding deceptive emails, websites, and messages that trick individuals into revealing personal data. Educating users on identifying phishing attempts and implementing security measures are essential to safeguarding against cyber threats.
multi-factor authentication
https://www.youtube.com/watch?v=zkkAL3w72go
Multi-factor authentication (MFA) enhances cybersecurity by requiring users to provide multiple forms of verification before accessing systems or data. This extra layer of security reduces the risk of unauthorized access, protecting sensitive information from cyber threats. MFA is crucial for safeguarding digital assets in today's interconnected world.
AI Report
Essay
Introduction
Cybersecurity is a crucial aspect of information technology (IT) that focuses on protecting computer systems and networks from unauthorized access, misuse, or damage. With the increasing reliance on technology in our daily lives, the threat of cyber attacks has become more prevalent than ever before. In this essay, we will discuss the importance of cybersecurity in the IT industry and the measures that can be taken to ensure the safety and security of sensitive information.
Body Paragraph 1
The growing number of cyber attacks has made cybersecurity a top priority for businesses, organizations, and governments worldwide. According to a report by Risk Based Security, there were over 5,000 data breaches in 2019, exposing more than 7.9 billion records. These attacks not only result in financial losses but also damage a company's reputation and erode customer trust. Hence, companies need to invest in robust cybersecurity measures to protect their assets and maintain their credibility.
Body Paragraph 2
One of the key elements of cybersecurity is network security, which involves securing the network infrastructure against potential threats. This can be achieved by implementing firewalls, intrusion detection systems, and data encryption techniques. Firewalls act as a barrier between a trusted internal network and external networks, filtering out malicious traffic. Intrusion detection systems monitor network traffic for any suspicious activity and alert IT teams in case of a potential threat. Encryption, on the other hand, protects sensitive data by converting it into a code that can only be deciphered by authorized individuals.
Body Paragraph 3
Another crucial aspect of cybersecurity is application security, which involves securing software and applications from potential threats. This is especially important in today's digital age, where almost every aspect of our lives is dependent on software and applications. Application security can be enhanced by conducting regular vulnerability assessments and penetration testing, identifying and fixing any weaknesses in the software code, and implementing secure coding practices.
Body Paragraph 4
Human error is one of the most common causes of cybersecurity breaches. Hence, it is essential to educate employees about cybersecurity best practices and the potential risks associated with negligent behavior. Companies should conduct regular training sessions to raise awareness about phishing scams, password management, and safe browsing practices. Additionally, implementing strict policies for data access and enforcing two-factor authentication can also help prevent unauthorized access.
Conclusion
In conclusion, cybersecurity is a critical aspect of IT that cannot be ignored. With the increasing sophistication of cyber attacks, companies must invest in robust security measures to protect their assets and maintain customer trust. Network security, application security, and employee training are some of the key elements that can help organizations stay one step ahead of cybercriminals. It is the responsibility of every individual to practice safe and responsible online behavior to ensure a secure digital landscape.
Lesson Plan
Lesson Title: Introduction to IT Cybersecurity and Maintenance
Grade Level: Technical Vocational Students (10th-12th grade)
Objective:
Students will be able to:
1. Define IT cybersecurity and its importance in the technology industry.
2. Identify different types of cybersecurity threats and how they can be prevented.
3. Understand the process of maintaining cybersecurity in an IT system.
Materials:
1. PowerPoint presentation
2. Handouts on cybersecurity terminology and types of threats
3. Whiteboard and markers
4. Computers with internet access
5. Online resources on cybersecurity maintenance procedures
Anticipatory Set (10 minutes):
1. Begin the lesson by asking students if they have ever heard of the term "cybersecurity" and what they know about it.
2. Show a short video or news clip about a recent cyber attack to pique students' interest and highlight the importance of cybersecurity in today's digital world.
3. Ask students to share their thoughts and opinions on the video.
Direct Instruction (25 minutes):
1. Define IT cybersecurity as the practice of protecting computer systems and networks from digital attacks and unauthorized access.
2. Explain the different types of cybersecurity threats such as viruses, malware, phishing, and social engineering and how they can harm an IT system.
3. Discuss the role of cybersecurity professionals in identifying and preventing these threats.
4. Introduce the concept of cybersecurity maintenance and its importance in keeping an IT system secure.
5. Explain the basic maintenance procedures such as regular software updates, data backups, and password management.
Guided Practice (15 minutes):
1. Divide students into groups of 3-4 and assign each group a specific type of cybersecurity threat.
2. Provide students with handouts on their assigned threat and ask them to research and come up with preventive measures for their assigned threat.
3. Each group will present their findings to the class and discuss how their assigned threat can be prevented.
Independent Practice (20 minutes):
1. Ask students to individually research and identify common cybersecurity maintenance procedures used in the industry.
2. Provide them with a list of questions to guide their research such as "What are the steps involved in updating software?" or "How can data backups be done effectively?"
3. Students will then create a step-by-step guide on how to maintain cybersecurity in an IT system using the information they gathered.
Closure (10 minutes):
1. Review the key points discussed in the lesson, emphasizing the importance of IT cybersecurity and maintenance.
2. Ask students to share their step-by-step guides with the class and discuss any differences or similarities.
3. Summarize the lesson by highlighting the main takeaways and answering any remaining questions from students.
Assessment:
1. Informal assessment during class discussions and group activities.
2. Review of students' step-by-step guides on IT cybersecurity maintenance.
3. Exit ticket where students write down the most important thing they learned about IT cybersecurity and maintenance.
Extension:
1. Invite a guest speaker from the IT industry to talk about their experience with cybersecurity and maintenance.
2. Assign a project where students create a cybersecurity plan for a hypothetical company or organization.
3. Encourage students to research and learn about different IT security certifications they can pursue in the future.
Class Syllabus Outline
Course Title: Introduction to IT Cybersecurity
Course Description:
This course provides an introduction to the fundamentals of IT cybersecurity. Students will learn about the various types of cyber threats and attacks, as well as the techniques and tools used to protect computer systems and networks. The course will cover topics such as risk assessment, vulnerability management, network security, and incident response. Students will also gain practical experience through hands-on exercises and case studies.
Course Objectives:
By the end of this course, students will be able to:
1. Define the key concepts and terminology related to IT cybersecurity.
2. Identify and classify different types of cyber threats and attacks.
3. Understand the techniques and tools used to protect computer systems and networks.
4. Perform risk assessments to identify potential vulnerabilities.
5. Develop a vulnerability management plan to mitigate risks.
6. Implement network security measures to secure data and communications.
7. Respond to security incidents and mitigate their impact.
8. Apply legal and ethical principles to IT cybersecurity.
Course Duration: 12 weeks (36 hours)
Prerequisites: Basic knowledge of computer systems and networks.
Course Outline:
Week 1: Introduction to IT Cybersecurity
- Definition of IT cybersecurity
- Importance of cybersecurity in today’s world
- Common cyber threats and attacks
Week 2: Risk Assessment
- Understanding risk assessment
- Identifying potential risks and vulnerabilities
- Risk management strategies
Week 3: Vulnerability Management
- Types of vulnerabilities
- Tools and techniques for vulnerability management
- Developing a vulnerability management plan
Week 4: Network Security
- Basics of network security
- Securing wireless networks
- Firewalls and intrusion detection systems
Week 5: Cryptography
- Principles of encryption and decryption
- Types of encryption algorithms
- Implementing cryptography for data protection
Week 6: Application Security
- Common application vulnerabilities
- Best practices for secure coding
- Web application security
Week 7: Identity and Access Management
- Understanding user authentication and authorization
- Role-based access control
- Implementing identity and access management in organizations
Week 8: Cloud Security
- Introduction to cloud computing
- Security considerations for cloud environments
- Securing data in the cloud
Week 9: Incident Response
- Identifying and responding to security incidents
- Malware detection and removal
- Forensics and investigation techniques
Week 10: Legal and Ethical Issues in Cybersecurity
- Laws and regulations related to cybersecurity
- Ethical considerations in cybersecurity
- Cybersecurity policies and procedures
Week 11: Security Audits and Compliance
- Types of security audits
- Compliance frameworks and standards
- Auditing techniques and tools
Week 12: Future of IT Cybersecurity
- Emerging technologies and their impact on cybersecurity
- Career opportunities in cybersecurity
- Final project and presentations
Course Delivery:
- Lectures and class discussions
- Hands-on exercises and case studies
- Group projects and presentations
- Guest speakers from industry experts
Assessment:
- Class participation and attendance – 10%
- Assignments and quizzes – 30%
- Group project – 20%
- Mid-term exam – 20%
- Final exam – 20%
Textbook:
Introduction to Cybersecurity, 2nd Edition by Timothy Shimeall, Jonathan Spring, and Corey Schou.
References:
1. Cybersecurity: The Essential Body of Knowledge by Dan Shoemaker and Wm. Arthur Conklin.
2. The Basics of Information Security: Understanding the Fundamentals of InfoSec in Theory and Practice by Jason Andress and Steve Winterfeld.
3. Cybersecurity: A Business Solution by Daniel Farber and Tom Farber.
Note: The course outline and schedule may be subject to change based on the progress and needs of the class.
Learning Objectives
1. Understand the basic principles and concepts of IT cybersecurity.
2. Identify and analyze potential cybersecurity threats and vulnerabilities.
3. Implement preventive measures and security protocols to protect computer systems and networks.
4. Utilize various tools and techniques for detecting and responding to cyber attacks.
5. Develop and implement effective risk management strategies.
6. Comply with legal and ethical standards related to cybersecurity.
7. Evaluate and select appropriate security solutions for different types of IT systems.
8. Monitor and maintain the security of computer systems and networks.
9. Apply best practices for data protection and privacy in IT environments.
10. Communicate effectively with team members and stakeholders regarding cybersecurity issues and solutions.
11. Conduct security audits and assessments to identify areas for improvement.
12. Stay updated on the latest trends and developments in the field of IT cybersecurity.
13. Demonstrate critical thinking and problem-solving skills in addressing cybersecurity challenges.
14. Collaborate with others to create and implement comprehensive cybersecurity plans.
15. Prepare and respond to cybersecurity incidents in a timely and effective manner.
Quiz Questions
1) What is the main purpose of a firewall in cybersecurity?
A) To block all incoming network traffic
B) To monitor and analyze network traffic
C) To prevent unauthorized access to a network
D) To encrypt all data transmissions
Answer: C) To prevent unauthorized access to a network
2) Which of the following is NOT a common type of cyber attack?
A) Phishing
B) Malware
C) Social engineering
D) Firewall breach
Answer: D) Firewall breach
3) Which of the following is a strong password?
A) Password123
B) P@$$w0rd
C) MyDogSpot1998
D) 12345678
Answer: B) P@$$w0rd
4) What is the purpose of encryption in cybersecurity?
A) To prevent data loss
B) To increase internet speed
C) To make data easier to access
D) To protect data from unauthorized access
Answer: D) To protect data from unauthorized access
5) What is the most common way for hackers to install malware on a computer?
A) Physical access to the computer
B) Through email attachments
C) Social media posts
D) Online shopping websites
Answer: B) Through email attachments